DocuSign Phishing Campaign
DocuSign has detected an increase in phishing emails sent to some of their customers and users – and has posted alerts on the DocuSign Trust Center and in social media.
The emails “spoofed” the DocuSign brand in an attempt to trick recipients into clicking a link which, when clicked, installs malicious software.
As part of their process in routine response to phishing incidents, DocuSign confirmed that DocuSign’s core eSignature service, envelopes and customer documents remain secure.
Out of an abundance of caution as a trusted brand and to protect customers from any further phishing incidents against their email, DocuSign recommends taking the following steps to ensure the security of your email and systems:
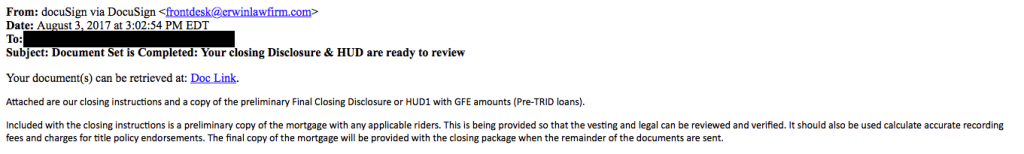
- Delete any emails with the subject line, “Document Set is Completed: Your closing Disclosure & HUD are ready to review” or “Completed: [domain name] – Wire transfer for recipient-name Document Ready for Signature” or “Completed [domain name/email address] – Accounting Invoice [Number] Document Ready for Signature”. These emails are not from DocuSign. They were sent by a malicious third party and contain a link to malware spam.
- Forward any suspicious emails related to DocuSign to spam@docusign.com, and then delete them from your computer. They may appear suspicious because you don’t recognize the sender, weren’t expecting a document to sign, contain misspellings (like “docusgn.com” without an ‘i’ or @docus.com), contain an attachment, or direct you to a link that starts with anything other than https://www.docusign.com or https://www.docusign.net.
- Ensure your anti-virus software is enabled and up to date.
- Review DocuSign’s whitepaper on phishing and share within your organization – it is available at https://trust.docusign.com/static/downloads/Combating_Phishing_WP_05082017.pdf
FRAUDULENT EMAIL SAMPLE:
VIEWS AND CONCLUSIONS EXPRESSED IN ARTICLES HEREIN ARE THOSE OF THE AUTHORS AND NOT NECESSARILY THOSE OF FLORIDA BAR STAFF, OFFICIALS, OR BOARD OF GOVERNORS OF THE FLORIDA BAR.